When considering the term “hackers,” the common perception is often of individuals seeking unauthorized access to computers to obtain passwords, steal identities, or cause general disruption. However, it is important to note that smartphones are also potential targets for these cyber threats, putting sensitive information at risk. Even with heightened precautions, the use of a Virtual Private Network (VPN) remains an advisable course of action to ensure security.
It is crucial to recognize the potential dangers of data breaches, as evidenced by recent incidents such as the Pegasus scandal. In these instances, cybercriminals may gain access to personal calls or messages, track location data, and even remotely activate microphones or cameras from any corner of the globe.
As the availability and usage of spyware tools expand among both authoritarian regimes and ordinary individuals, the need to safeguard personal mobile devices against potential hacks is paramount. It is crucial to maintain good digital hygiene practices and be equipped with knowledge to secure one’s smartphone defenses, as well as knowing how to recognize signs of a possible hack.
This article seeks to provide comprehensive guidance on two key areas. Firstly, preventative measures to stop unauthorized access to mobile data, and secondly, a step-by-step guide on what actions to take if a hack is suspected or confirmed.
Related: TikTok faces global backlash and Danish ban
Common tactics that hackers use
Phishing
Phishing is a deceptive tactic that involves the transmission of malicious links and/or harmful attachments through emails and text messages. By clicking on such links, the victim’s mobile device may become infected with malware that can be used to extract sensitive information.
Spyware
Hackers can also leverage spyware software to collect data by deploying tracking apps. These applications are often easy to install and operate, making it possible for anyone to spy on your phone with relative ease.
Public networks
Infiltrating public Wi-Fi and Bluetooth networks presents yet another vulnerability. When connecting to public Wi-Fi networks, personal data is potentially exposed. To mitigate this risk, it is recommended to use a reliable mobile VPN service. Bluetooth connections can also be breached by hackers seeking to gain unauthorized access to mobile devices.
Sim swapping
Another technique employed by malicious actors is sim swapping, whereby they transfer a victim’s phone number to their own SIM card, thereby taking control of the victim’s accounts.
How do you safeguard your phone from hackers?
To safeguard your mobile data from malicious actors, it is crucial to follow certain best practices for digital hygiene. The following actions can help bolster your mobile device security.
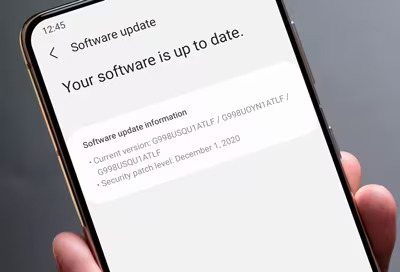
Stay up-to-date with software updates
Hackers frequently exploit vulnerabilities in software to gain access to mobile data. To mitigate the risk, always ensure that your device runs the most updated software version.
Manage app permissions
Even seemingly innocuous apps can collect sensitive data, such as location or microphone/camera access. It is advisable to grant app permissions only for essential functions and review app settings periodically.
Use mobile antivirus software
While iPhones may not require antivirus protection, Android users can benefit from using antivirus apps. These apps can detect and remove malware, as well as prevent access to malicious web pages and downloads.
Use a VPN on any public network
Public Wi-Fi networks can be a common entry point for hackers. To protect your mobile data, use a VPN service when connecting to open wireless networks. This will help secure your data by encrypting it and masking your IP address and location.
Avoid all auto-login features
It can be tempting to use auto-login features for convenience, but this can pose a risk if a cybercriminal gains access to your phone. It is advisable to avoid auto-login for sensitive applications and use unique passwords for each app. Consider using a password management software to help manage passwords securely.
Secure physical access to your phone
Physical access to your smartphone can be a vulnerability, so it is essential to take measures to prevent unauthorized access. Always set a six-digit passcode to access the device and avoid leaving your phone unattended in public places. Passcodes are more secure than biometric options such as facial recognition or fingerprints.
Enable ‘Find my device’
If your phone is lost or stolen, being able to locate and erase data remotely is essential. Enable ‘Find my device’ services provided by Apple and Google to locate your phone on a map and erase sensitive data if necessary.
Disable your voice assistant on your lock screen
While voice assistants such as Siri and Google Assistant can be convenient, they can also pose a risk to mobile data security. Disabling the voice assistant option on the lock screen can help prevent unauthorized access to your contacts, chats, emails, and calls.
Avoid of public charging stations
Public charging stations can be a convenient solution to low battery levels but pose a risk of data breaches. Cybercriminals can access your phone’s data or introduce malware through a USB drive. It is advisable to use AC charging ports instead, as they transmit only power rather than data. Alternatively, consider using charge-only adapters and data blockers to prevent data breaches.
What to do if you get hacked
If you suspect that your phone has been hacked, there are several actions you can take to mitigate the situation.
Run antivirus software
It is recommended that you install and operate trustworthy antivirus software on your mobile device to remove any existing threats. Furthermore, ensure that the software remains active and updated to prevent the occurrence of future security breaches.

Secure your credit card information
To safeguard your financial information, it is advisable to monitor your credit card transactions regularly and report any suspicious activity to your bank immediately. In the event of any anomaly, consider blocking your card and notifying the bank to prevent unauthorized access. Additionally, contact e-commerce businesses that store your credit card or bank account information on your phone app to verify and safeguard against any potential fraudulent activity.
Delete untrustworthy apps
It is recommended that you review all the applications installed on your mobile device and remove any suspicious ones to prevent hackers from gaining unauthorized access. Conducting periodic checks for suspicious apps is an essential aspect of maintaining mobile device security.
Reset your device
To ensure that your mobile device is free from malware and potentially harmful applications, consider performing a factory reset after backing up essential data. This process will remove all data, malware, and potentially harmful apps from the device, restoring it to its original settings. It is important to note that this step is irreversible, and all data, including photos, contacts, and messages, will be deleted. Therefore, it is crucial to back up all essential information before proceeding with a factory reset.

Change all your passwords
To safeguard against data breaches that may have occurred due to a mobile device hack, it is essential to change all login credentials for your various online accounts. This will help prevent unauthorized access to your personal information and minimize the risk of identity theft. It is crucial to choose strong, unique passwords and enable two-factor authentication wherever possible to enhance account security.
Report to authorities
If you have been a victim of identity theft or feel threatened as a result of a mobile device hack, it is crucial to report the incident to the relevant authorities responsible for investigating digital crimes in your country. In the United States, victims of identity theft can report the incident to the Federal Trade Commission, while in the United Kingdom, Action Fraud is the national fraud and internet crime reporting center. Reporting the incident can help law enforcement officials investigate and potentially apprehend cybercriminals, as well as prevent further damage to your personal information.
Related: WhatsApp takes on the EU over encryption and child abuse content
Advertisement
