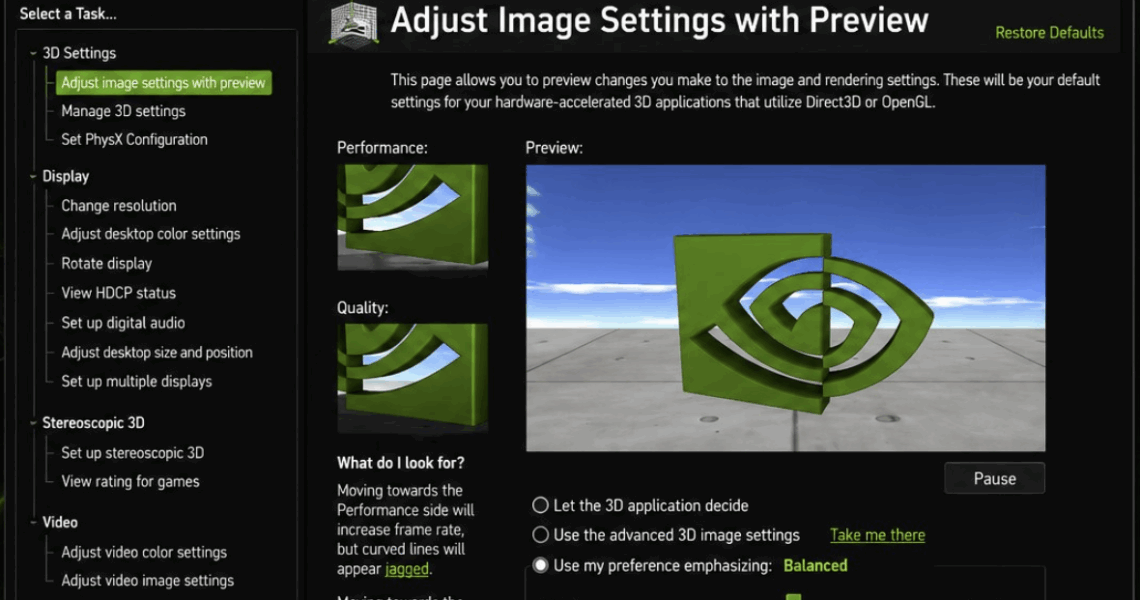
NVIDIA Officially Retires Control Panel After 20 Years in Favor of NVIDIA App
2026-05-27NVIDIA has officially retired the NVIDIA Control Panel after 20 years, the company announced in a GeForce Driver blog post for 007 First Light. The shutdown applies to both Game Ready and Studio Drivers. NVIDIA RTX PRO users will continue to receive support for the Control Panel until professional features are moved to the NVIDIA […]